Quote from: Cain on March 30, 2015, 01:58:22 PM
And "I then realised PD was not impressed with my translated reposts from my Livejournal, and I would need to try harder to obtain my guru status".
by the way, check out this thread
Testimonial: "PD is the home of Pure Evil and All That Is Wrong With the Interwebz." - Queen of the Ryche, apparently in all seriousness
This section allows you to view all posts made by this member. Note that you can only see posts made in areas you currently have access to.
Show posts MenuQuote from: Cain on March 30, 2015, 01:58:22 PM
And "I then realised PD was not impressed with my translated reposts from my Livejournal, and I would need to try harder to obtain my guru status".
Quote from: The Johnny on March 30, 2015, 08:44:11 PMYou seem to have a fetish fir the word "forge" and derivatives.
And I hope this doesn't offend you but your thoughts seem disparate, have you been taking your pills?
Quote from: Cain on March 30, 2015, 01:58:22 PM
And "I then realised PD was not impressed with my translated reposts from my Livejournal, and I would need to try harder to obtain my guru status".
Quote from: Doktor Howl on March 30, 2015, 03:13:07 PM
My only concern is whether or not he's a hipster trying to be Grant Morrison, or someone with actual mental problems.




Quote from: LMNO, PhD (life continues) on March 27, 2015, 06:22:58 PM
In that case, whistlestomp head swipe, mango aardvark detritus.
Quote from: LMNO, PhD (life continues) on March 27, 2015, 03:57:59 PM
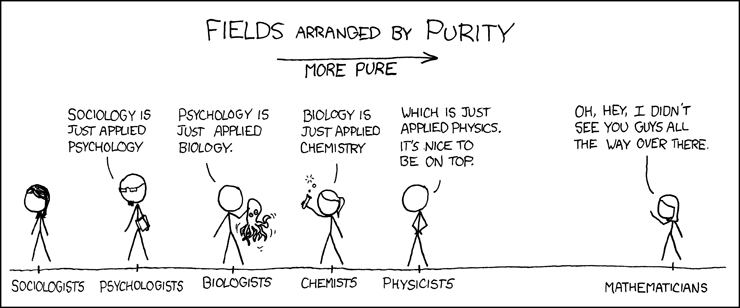
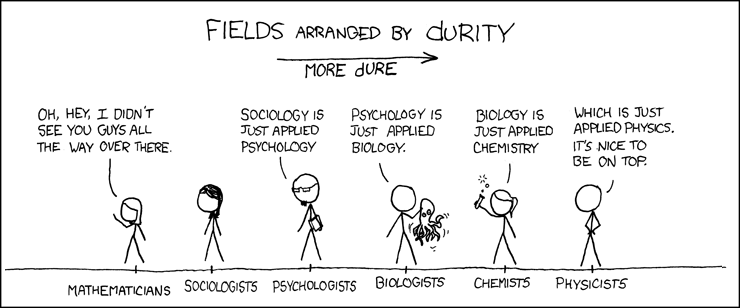
Incidentally, "durity" means "obsolete", so you're saying that physicists are more obsolete than mathematicians. Is that what you meant to say?
Quote from: Cainad (dec.) on March 24, 2015, 12:54:03 PM
So how, pray tell, do you propose that we take ownership over the source of our own thoughts?
Quote from: Doktor Howl on March 23, 2015, 05:21:33 PM
Have you ever owned a pet?
Quote from: Sung Low on March 22, 2015, 10:21:35 PMIs forgery not an attempt to pass off an imitation as the real eal for personal gain?
Quote from: Prince-of-Plots on March 22, 2015, 09:00:19 PMAlso, there are historical accounts of Stonehenge going back to the 11th century, and it was subjected to substansial restoration work - not removal - from the 1890s to the 1950s.


